Abstract
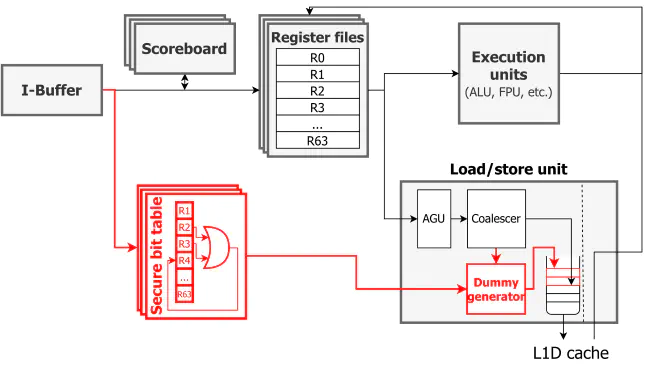
Architectural considerations for secure executions are getting more critical for GPU since popular security applications and libraries have been ported to a GPU domain to rely on GPU’s massively parallel computations. Recent studies disclosed the security attack models that exploit GPU’s architectural vulnerabilities to leak the secret keys of AES. The attack models exploit the high correlations between the execution time of a kernel and the number of memory requests generated from memory coalescing. Thus the prior architectural defenses provide secure executions by randomizing or restricting the memory coalescing from load warps. However, those defense approaches result in significant performance overhead since memory coalescing is an essential feature for improving the performance of GPU. In this paper, we propose GhostLeg, an efficient architectural defense approach against correlation-based GPU security attacks. GhostLeg selectively applies secure executions for load warps to minimize performance overhead induced by concealing memory coalescing behavior. Our analysis of AES reveals that only the load warps whose index addresses are influenced by secret keys are vulnerable to security attacks. In order to minimize the performance overhead by secure executions, GhostLeg pinpoints the load warps that require secure executions based on the class of a source register. The secure flag assigned to each register can be set by propagation from non-deterministic user data (GhostLeg-ND) or a specific directive marked by programmers (GhostLeg-Key). Our evaluation shows that GhostLeg guarantees secure executions against the correlation-based attacks and GhostLeg-ND exhibits 54.7% higher performance compared to the state-of-the-art GPU defense solution.